Proxy / VPN Detection - passive fingerprinting methods

What is Proxy / VPN Detection ?
These tools are used for passive analysis of the TCP/IP stack on the server side. By examining the data packets coming from you, the server can determine whether or not you're using a Proxy/VPN as well as your operating system, the connection type and number of network nodes, your system uptime, and other information.
What is MTU and MSS?
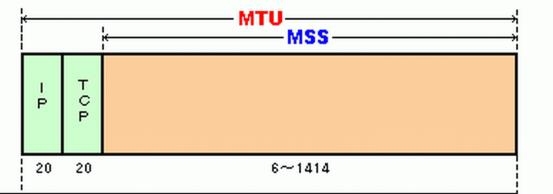
MTU (Maximum Transmission Unit) sets the upper size limit of an IP packet (including the header) being sent over the network.
MSS (Maximum Segment Size) sets the upper size limit of the data unit being transmitted (excluding the header length).
The MTU to MSS ratio in the settings of your network adapter can be used to optimize the available bandwidth for faster data transfer.
How the MTU / MSS settings can reveal the use of a proxy / VPN server?
When your device connects to the server directly, the MTU is set to a standard value (for example, 1500 for Ethernet or 1480 for PPTP). When connecting through a Proxy/VPN via protocols like PPTP, L2TP (± Ipsec), or IPsec IKE, original packets are placed inside other packets (encapsulated), resulting in increased packet size. To prevent excessive packet fragmentation and maintain good data transfer speed, the operating system lowers the MTU setting at the network interface (e. g., to 1400 for IPsec).
When a connection uses the OpenVPN software, the system leaves the MTU setting unchanged but can change the size of MSS within the packet instead.
By comparing the packet size within an intercepted connection to a table of standard MTU / MSS settings, the use of a proxy or VPN can be detected.
How to protect your anonymity from MTU / MSS detection methods?
Just manually edit MTU / MSS parameters for your network interface.

 Russian
Russian